Table of contents
- Why Your Offshore Backend is a 2026 Security and Liability Time Bomb
- The Architecture Vacuum
- The Compliance Nightmare
- The "Premium Transformation" Grift
- The Nest Software Standard
- CTO Checklist: 5 Non-Negotiables for Your Next Backend Hire
- Frequently Asked Questions
- Stop Hiring Coders. Start Hiring Architects.
Beyond the Code: Why Your Offshore Backend is a 2026 Security and Liability Time Bomb

You’ve been burned before. Maybe not publicly—maybe it was the quiet kind, the kind where your VP of Engineering pulls you aside on a Friday afternoon and explains that the offshore team’s “completed” microservices architecture needs a full rewrite. Or maybe it was louder: a compliance audit that uncovered unsupported operating systems sitting on your production network, a breach notification you had to draft at 2 AM, a board meeting where you explained why the product launch failed for the third consecutive quarter.
If you’re reading this in 2026, the calculus has shifted. The 2020-era pitch—”save 60% on developer costs by going offshore”—has collided with a regulatory environment, threat landscape, and technical debt crisis that makes raw cost savings irrelevant if your backend infrastructure is a liability waiting to detonate.
Here’s the premise that most outsourcing discussions still refuse to confront: offshore backend development doesn’t fail at the syntax level. Your offshore team can write functioning Python. They can stand up a Django REST framework. The failure happens at the governance and architecture level—where nobody is asking why the system is designed this way, whether it will survive its first real security audit, or who owns the decision to skip input validation on that internal API endpoint because “it’s just for internal use.”
The industry spent years chasing the “cheap developer” myth. Now it’s paying for it. A Fortune 500 procurement team recently spent six months evaluating “AI-powered transformation consultants” who turned out to be offshore developers with a ChatGPT wrapper. Two million dollars later, they had what $50,000 of actual engineering would have delivered. That’s not an anecdote. That’s the pattern.
The Architecture Vacuum: Why Your "Invisible" Backend Infrastructure is Bleeding Value
Backend infrastructure fails silently before it fails catastrophically. The oversight gap in offshore development isn’t about time zones or language barriers—it’s about the absence of colocated architectural governance. When no senior architect is embedded with the team making daily design decisions, those decisions default to the path of least resistance: copy-paste patterns from Stack Overflow, monolithic database schemas that “work for now,” and API contracts that nobody documented because nobody asked.
This isn’t theoretical.
Forrester predicts that over 50% of tech decision-makers will face moderate-to-high technical debt severity in 2025, escalating to 75% by 2026—fueled directly by rushed AI adoption and outsourcing arrangements that skip architecture ownership entirely. Gartner’s parallel forecast is grimmer: 75% of organizations will face systemic failures from unmanaged technical debt by 2027. That number isn’t a rounding error. It’s the aggregate price of every shortcut, every undocumented service, every “we’ll refactor later” that never got refactored.
The credential inflation problem compounds this. As one engineering leader recently highlighted in a viral discussion:
“Entire companies are being populated from offshore agencies. It’s easier to drain the company when the oversight is not in the country. Failed launch after failed launch—and the grift goes all the way to the board.”
— Verified engineering thread, X · 384 likes, 52 reposts · Feb 2026
The result isn’t just bad hires; it’s failed product launches, cascading architectural failures, and brittle, unmaintainable backends that repeatedly kill product velocity.
When we audit backend infrastructure at Nest Software, the pattern is almost always the same. The code compiles. The tests pass (when tests exist). But the system design reveals no evidence of trade-off reasoning—no documentation of why PostgreSQL was chosen over DynamoDB for a write-heavy workload, no capacity planning, no consideration of failure modes. The team shipped features. Nobody shipped architecture.
The gap between “working code” and “maintainable, scalable infrastructure” is where your valuation lives or dies. And that gap is invisible until it isn’t.
The Compliance Nightmare: When "Cost-Cutting" Infrastructure Hacks Lead to a Multi-Million Dollar Breach
A recent scenario surfaced online that should make every CTO’s stomach drop:
Field Report · Verified Engineering Thread: “Had a company outsourcing their IT to India… noted a Windows XP system on the main network. Other experiences included modifying VMware to run on unapproved hardware and running vCenter on less than minimum specs to save a buck. The security threat is real.”
Not a lab environment. Not a sandboxed legacy system. The main network. Offshore agencies operating on razor-thin margins routinely bypass security baselines and compliance standards to hit cost targets. Every one of these shortcuts creates a persistent attack surface that your in-house security team doesn’t know exists until an attacker finds it first.
The remote access problem is structural, not procedural. A security-focused thread laid out the reality with uncomfortable precision: supporting internal networks from offshore requires secure remote access through multiple firewalls to Azure VNets with Network Security Groups, or AWS VPCs with Security Groups and Network Access Control Lists, followed by additional firewall layers for database access requiring key rotation and secrets management in segregated virtual networks. Each layer demands precise configuration, real-time monitoring, and personnel who understand why each rule exists.
Under timezone gaps, process fragmentation, and cost pressure, these controls fail. Not occasionally. Predictably.
The Cognizant-TriZetto breach is the case study every CTO should have pinned to their wall. In October 2025, Cognizant’s TriZetto Provider Solutions subsidiary disclosed a breach exposing data belonging to 3.4 million people—including Social Security numbers and protected health information. The unauthorized access dated back to November 2024. Nearly a year of undetected intrusion. Class-action lawsuits followed. The breach didn’t happen because Cognizant employed bad programmers. It happened because multi-layered vendor monitoring failed at scale.
Verizon’s 2025 Data Breach Investigations Report confirms this isn’t an outlier. Analyzing over 22,000 incidents, the report found that third-party involvement—vendors, partners, offshore teams—doubled year-over-year to 30% of all breaches, up from 15%. Third-party identity management now equals regulatory compliance as a priority for security leaders.
Your API gateway, your database credentials, your internal service mesh—if the team managing them treats NSG rules as optional and key rotation as “something we’ll get to,” you don’t have a backend. You have a breach in progress.
The "Premium Transformation" Grift: Spotting ChatGPT Wrappers vs. Actual Engineering
The $2 million ChatGPT wrapper story isn’t funny. It’s a procurement failure pattern that’s accelerating in 2026 as agencies rebrand commodity offshore capacity as “AI-powered enterprise transformation.”
Here’s what that looks like in practice: an agency presents a polished slide deck featuring machine learning pipelines. The deliverable, six months and seven figures later, is a REST API that calls OpenAI’s GPT-4 endpoint, wraps the response in a branded JSON schema, and returns it to the client’s frontend. Just an API key and a prayer.
A working API endpoint that returns the correct data is table stakes. A production-grade API endpoint requires OAuth 2.0 or OpenID Connect for authentication, JWT tokens with proper expiration, role-based access controls, rate limiting, input validation, and audit logging. When we evaluate offshore-delivered backends at Nest Software, the API layer is usually where the rot is most visible. The team delivered the feature. Nobody delivered the security posture.
The hidden liability math is straightforward. A backend delivered without security-by-default design costs X today. The in-house rewrite to make it compliant with GDPR, SOC 2, the EU AI Act, or the Cyber Resilience Act costs 10X tomorrow. The agency that delivered at $80/hour has long since been paid. The in-house team that fixes the architecture at $200/hour—across three months—is the actual cost of the original decision. And the breach that happens in the interim costs 100X.
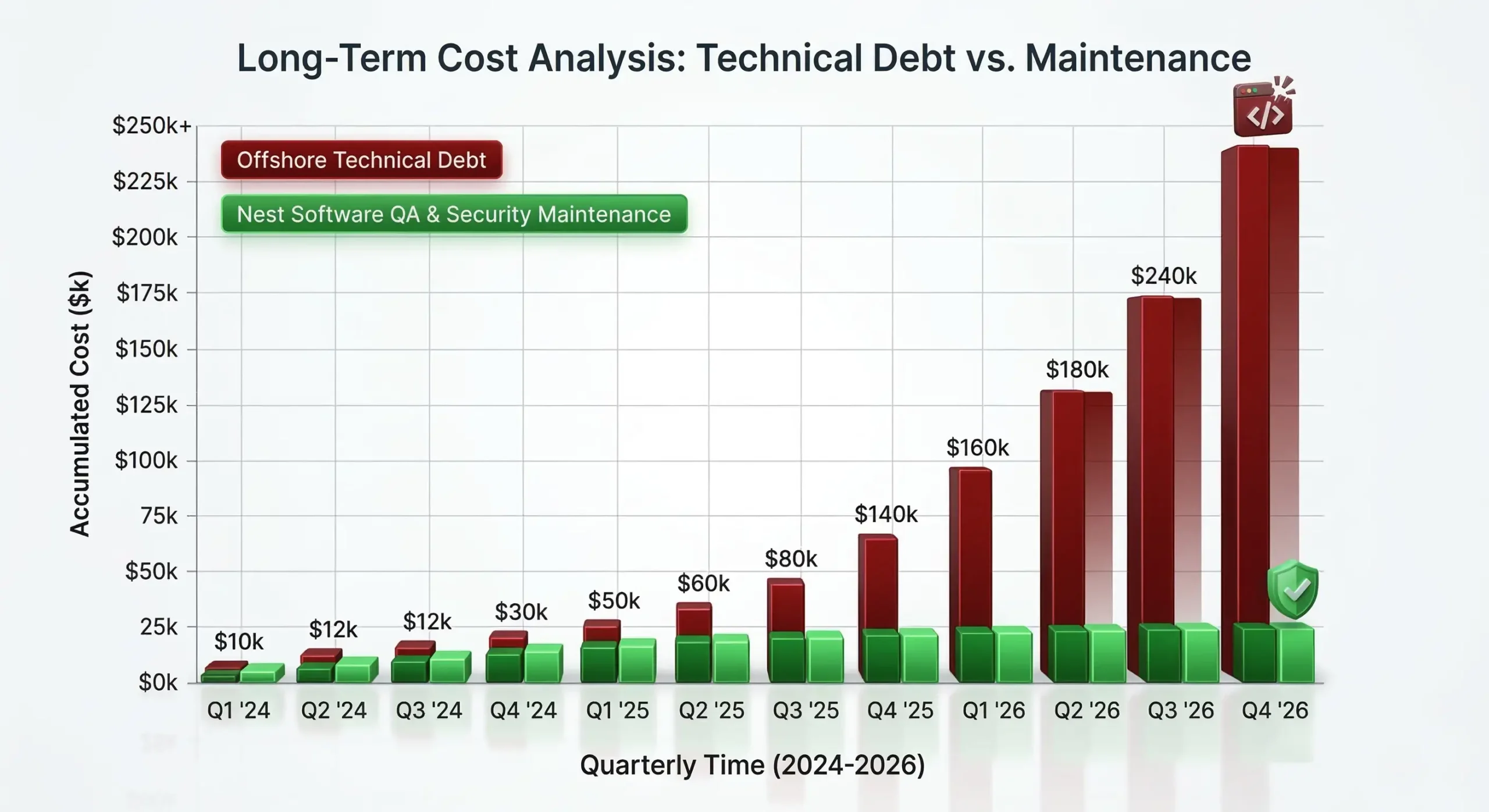
Cheap code is the most expensive mistake a CTO can make. Figure 1 shows the inevitable 10x price tag of fixing bad backend infrastructure versus the flat, manageable cost of Nest Software’s ‘Secure-by-Default’ model.”
The Nest Software Standard: Bridging the Governance Gap with "Vetted Architectural Ownership"
Staff augmentation—hiring bodies to fill seats and write code to spec—is the model that created every problem described above. At Nest Software, we rejected that model. What we provide instead is architectural ownership: senior engineers who don’t just execute tickets but interrogate requirements, flag design pitfalls before they become bottlenecks, and take accountability for the long-term maintainability of every system they touch.
- System Design Reasoning: Every backend developer at Nest Software undergoes live system design evaluation—real-time assessment of how they reason through trade-offs under constraints.
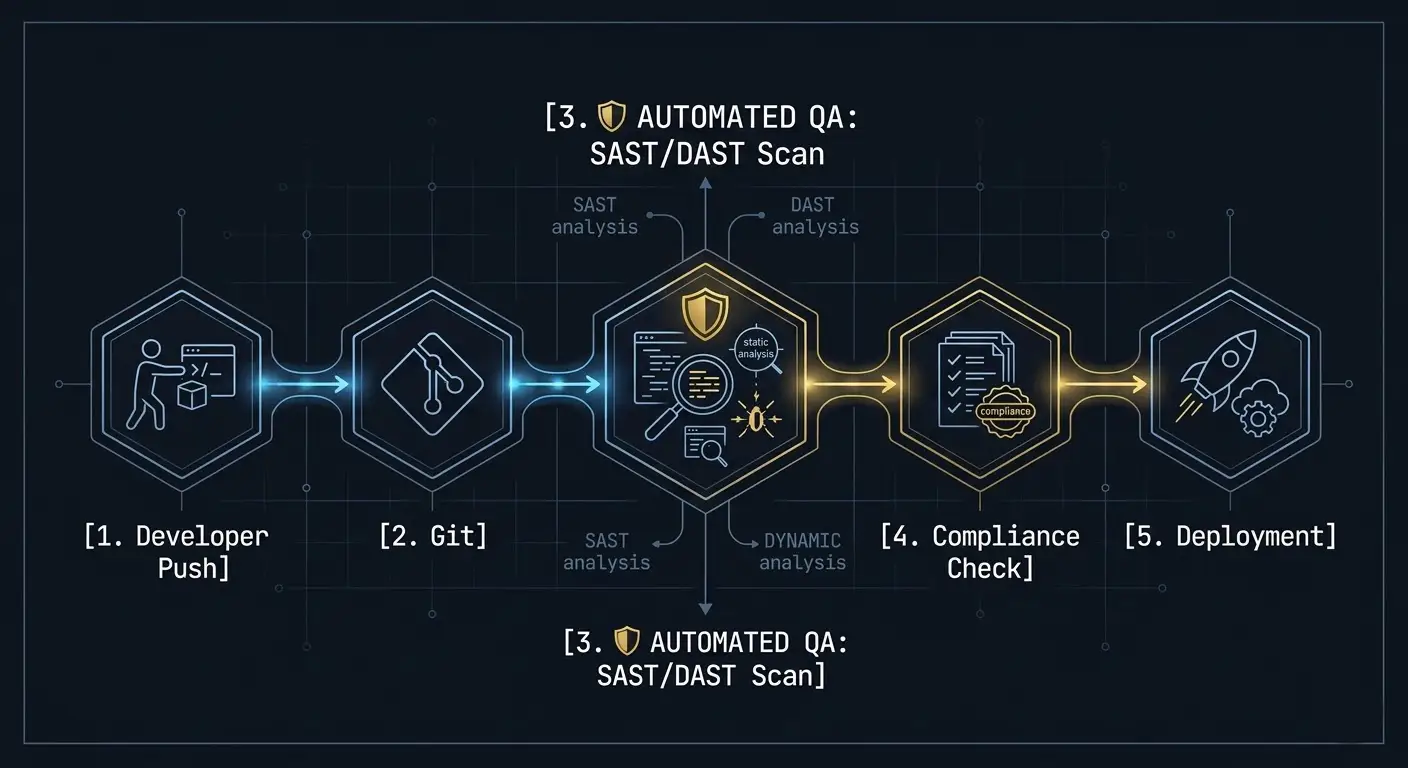
- Security-First Mandate: Secrets management using tools like HashiCorp Vault or AWS Secrets Manager is enforced from day one. Every deployment includes automated vulnerability scanning (SAST and DAST) integrated into CI/CD pipelines.
- Test-Driven Development: TDD is a delivery requirement. Every function ships with tests that verify correctness and create an audit trail.
- Regulatory Alignment: Nest Software aligns every backend engagement with 2026 regulatory realities from project kickoff—because retrofitting compliance into a system designed without it is the most expensive engineering work that exists.
Cognizant’s own 2025 annual report flagged reputational and operational risks from heavy offshore outsourcing, including data misuse and regulatory exposure. We read that report as a confirmation of what we’ve built our practice to prevent.
CTO Checklist: 5 Non-Negotiables for Your Next Backend Hire
- Auditability: Can they provide a complete, timestamped audit trail for every infrastructure change (security groups, IAM policies, secrets access)?
- Security Baselines: Do they use automated vulnerability scanning integrated into their CI/CD pipeline running on every pull request?
- Architectural Ownership: Do they proactively flag design pitfalls before those pitfalls become production bottlenecks?
- Performance Engineering: Can they optimize for sub-two-second server response times and Core Web Vitals compliance?

Frequently Asked Questions
How do I prevent technical debt when outsourcing backend development?
What are the biggest security risks with offshore IT teams in 2026?
How can I verify the credentials of offshore backend developers?
Is India still a viable destination for enterprise-grade backend development?
What is the impact of the Cognizant-TriZetto breach on IT outsourcing?
Stop Hiring Coders. Start Hiring Architects.
Every statistic in this article points to the same conclusion: the risk profile of offshore backend development has fundamentally changed, and the vendors who built their businesses on cost arbitrage haven’t changed with it. Your backend infrastructure isn’t a cost center. It’s the attack surface, the compliance surface, and the scalability surface of your entire business.
At Nest Software, we build backend systems the way your board, your auditors, and your customers demand: secure by default, auditable by design, and owned by senior engineers who understand that architecture decisions made today determine whether your company thrives or scrambles in 2027.
We’re not the cheapest option. We’re the option that doesn’t cost you 10X next year.
Hire Vetted Senior Backend Developers from Nest Software Today

